Aljamed ... the zero trust framework assumes there is risk unless proven otherwise
Aljamed ... the zero trust framework assumes there is risk unless proven otherwise
Energy and critical infrastructure companies, need to adopt forward looking cybersecurity policies like zero trust to protect their operations, explains Khalid Aljamed, Regional Director for Middle East and Africa, Nozomi Networks
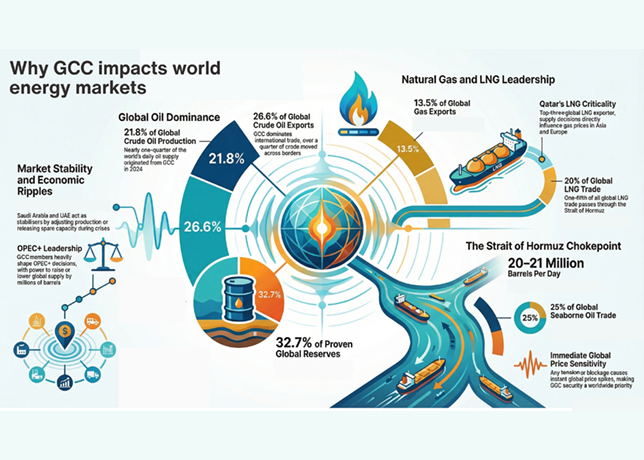
A nation’s essential services, which includes energy, are classified as critical national infrastructure. As an example, in the US there are 16 critical infrastructure sectors, and, in the UK, there are 13 listed. If any of these infrastructures were to be compromised, there would be widespread disruption and potential danger to life.
Within critical national infrastructure organisations, it has traditionally been that IT teams have been tasked with protecting the infrastructure from cyber security threats, whereas engineering and operational teams have taken care of managing operational technology.
However, as operational technology (OT) within industrial plants has grown increasingly connected, this has resulted in the convergence of two traditionally siloed departments.
OT has historically been designed without cyber security in mind, and security concerns have previously focused only on preventing physical access. However, modern industrial plants regularly connect machines, devices, sensors and people to the internet.
The use of the industrial internet of things (IIoT), which involves connecting smart devices and using the data collected to increase efficiency in production and cost has eliminated the security blanket of a fully air-gapped OT environment.
To benefit from increased connectivity within critical national infrastructure, all connected devices and networks must be secure.
The strength of this security will determine how vulnerable critical national infrastructure is to a cyberattack.
One such approach is the zero trust framework that disallows connectivity by assuming there is risk unless proven otherwise.
Rather than simply defining a minimalist access policy, security posture and context can play a role in improving zero trust security. This helps significantly reduce risk by making more informed decisions about connectivity.
Zero trust switches the mindset toward the network from allowing access by default, to blocking access by default unless required and explicitly allowed.
WHAT DOES IT REALLY IMPLY?
Context is very important for zero trust policies. A zero trust architecture, prior to allowing a machine or user to connect to the network, should verify whether that connection can be made safely.
The connection should be established between the minimum number of resources that are needed. These checks should be done on a per-session basis instead of once-off at the start.
Incorporating context into zero trust policy decisions stands in stark contrast to the usual allow list approach of zero trust implementations. Obviously, identity is important to verify but it still does not really help assess whether the connection can be made safely and should be allowed, especially if the device has been compromised.
ZERO TRUST FOR OT-IOT
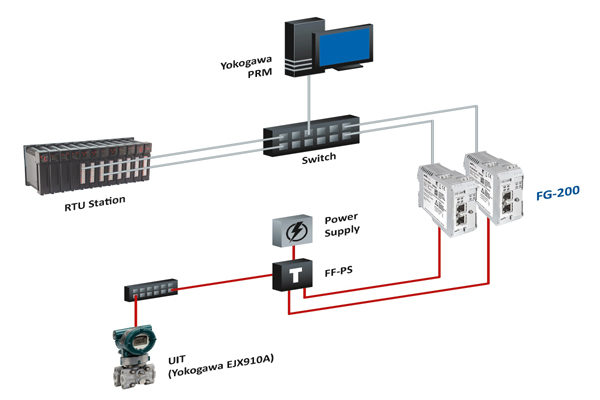
The convergence of IT/OT means that the protection against these types of attacks previously offered by air-gapped industrial control systems in energy companies is now obsolete.
The increasing connectivity of industrial control systems and SCADA systems has opened critical national infrastructure to cyberattacks that would have previously been isolated to IT systems.
In the US, over 3,000 utility companies work together to deliver power through over 321,000 km of high voltage transmission lines.
Millions of homes and businesses are powered by 55,000 electrical substations and 5.5 million miles of distribution lines. An attack on any of these grids would leave millions of people without power, causing widespread disruption and potential loss of life.
Here is a basic check list:
• Does micro-segmentation make sense for OT?
• What about user agents?
• Where do you start?
• What if traffic is blocked?
• What impact will that have on the process?
It is totally normal in IT to block traffic, but in OT-IoT this is risky. Simply blocking it might just impact production more than allowing traffic.
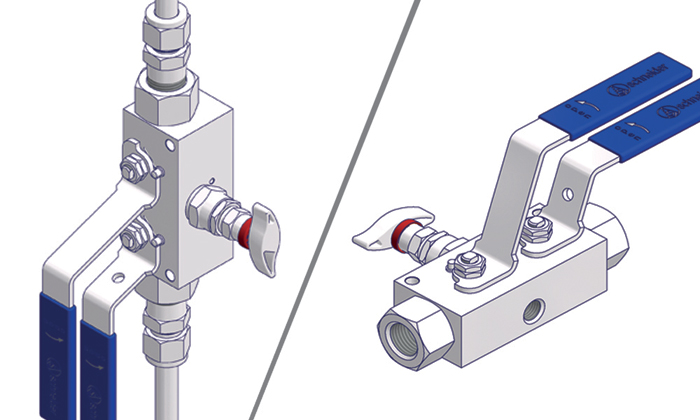
Many OT-IoT devices like controllers, sensors, robots, and so forth are headless. Very often, security was not a consideration when these products were developed.
To make better-quality decisions about connectivity, you need better information.
Understanding what you are trying to protect is where it all starts. It is identical to IT, but the methods of getting there just differ.
This is about knowing the type of devices, what hardware and software is used and what the expected behavior of those devices is. This is about knowing how the entire OT-IoT environment behaves, which machine speaks to another machine? With what protocol? What payload is exchanged? At what frequency?
If you understand this in real-time, you are well on your way towards an optimal zero trust for OT-IoT environments.
DECISION-MAKING FOR OT-IOT
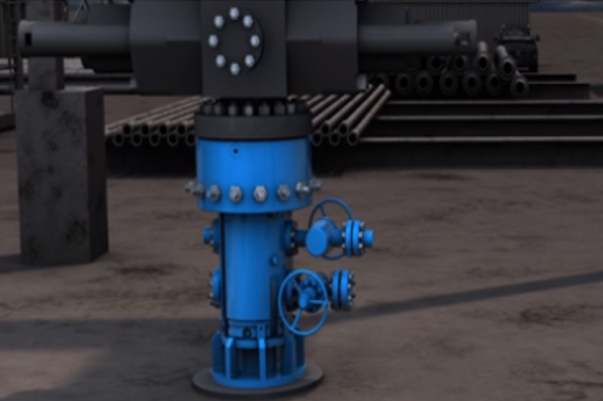
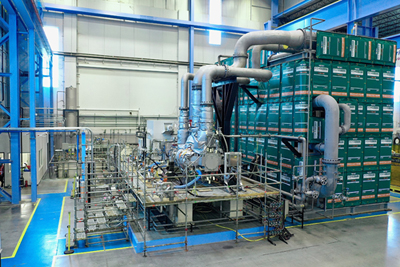
 |
The security of Critical infrastructure is an area of concern |
Gathering information must lead somewhere; it should be converted into actionable intelligence and ultimately actions.
Knowing hardware and software versions will lead to knowing what vulnerabilities apply to those monitored devices, whether those devices are even still supported by their vendors, and how they should act on the network.
Knowing the behaviour of entire OT-IoT networks inside energy and utility companies also implies the ability to detect and alert upon anomalies.
If, suddenly, devices that never communicated with one another start doing so or if there was communications before, but it is now displaying entirely different behavior, it justifies investigation into the legitimacy of it. It is very possible that this is the start of a breach.
Energy operators should endeavour to have real-time visibility of their networks that will allow them to rapidly detect anomalies using machine learning and artificial intelligence. These technologies can passively monitor network activity and traffic to identify suspicious activity and stop attacks quickly.
In addition, energy companies should identify all the devices connected to their network, ensuring that all are secure.
A vulnerability management programme can aid organisations in identifying vulnerabilities that need to be patched or mitigated.
This will allow operates to access their cyber risk and take appropriate action to secure CNI.
It is crucial that any vulnerabilities that are detected are patched or mitigated quickly to avoid unauthorised access to industrial systems.
Data gathered towards zero trust should not just be a few lines stating what the likely issue is; it should help determine what impact it has on the entire OT-IoT network.
With regards to enforcement of a zero trust policy, even in OT-IoT, sometimes it is justified to automate interventions by blocking traffic.
The suite of tools that form the cyber defence mechanism should play nice and exchange information to act as fast as possible so each can fulfil its function effectively.
Coordination and intelligence sharing between government and private enterprises will be crucial for effective navigation of an increasingly complex and sophisticated threat landscape.
The sharing of information on evolving threats will help energy organisations implement the necessary strategies needed for securing critical infrastructure from the inside out.
Today’s attackers, whether they are cyber criminals or nation-states, do not appear to be slowing down.
However, the more we learn and understand about attackers’ playbook, the greater chance we have to put ourselves a step ahead of the bad guys.
Pairing all of this with digital transformation in OT-IoT and we have a perfect storm on our hands, which a zero-trust approach can help to mitigate.