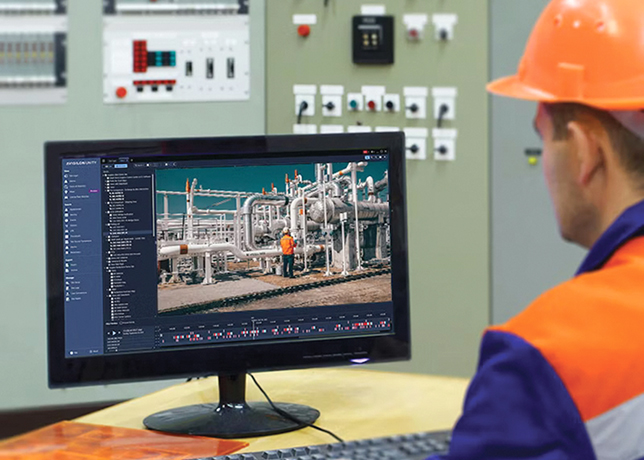
Monitoring the place where cybercriminals conduct operations can greatly reduce the impact of threats and disruption to operations, Dr Gareth Owenson, Co-Founder and CTO of Searchlight Cyber, tells OGN
Companies around the globe are uniquely attuned to the threat – and potential impact – of a cyberattack. At $7.46 million per breach, the Middle East has the second highest average total cost of a data breach in the world.
In part, because the energy sector is particularly lucrative and therefore attractive to cybercriminals, as witnessed in the 2012 attacks on Saudi Aramco’s and RasGas's computer systems.
As these attacks often originate on the dark web, visibility and monitoring of this secretive part of the internet – where sensitive company data and access information is sold to the highest bidder – is essential.
A REAL AND GROWING THREAT
 |
|
Graph 1 ... giving away details to attackers |
When a breached employee email account sold on the dark web leads to mass panic, raised petrol prices and widespread gas shortages, it becomes unavoidably clear how much harm cybercriminals can do.
This was the case with the infamous Colonial Pipeline ransomware attack of 2021, which led to the declaration of an emergency in 17 US states and sent shockwaves around the world. This likely started with a password from a breached employee email account being sold on the dark web.
However, there remains widespread misconceptions about what the dark web is, how cybercriminals use it, and how their activity could impact energy organisations in the future.
THE PLACE CYBERCRIMINALS CALL HOME
The dark web is an unregulated, purposefully hidden away corner of the internet. Unlike the ‘clear web’ (the internet we use to search and look up information daily), the dark web cannot be accessed by conventional browsers and its pages don’t show up in standard search engines. To reach it requires downloading specialised software and knowing exact domain addresses.
The dark web has been around for decades, and those involved in illegal activity there frequent hacking forums where techniques and tools like exploits and malware are discussed.
The dark web has also exploded as a commercial marketplace in the cryptocurrency era to become a place where criminals buy and sell everything from company network access and email logins to confidential documents to drugs.
 |
|
Graph 2 ... initial access broker post |
However, despite what criminals think, the dark web does not provide blanket anonymity. Security teams and law enforcement can gain visibility into what happens there. Seeing who is targeting them - and how - is invaluable intelligence for energy companies.
EYES ON THE ENERGY SECTOR
Cybercriminals use the dark web to plan attacks on organisations in every industry, including the energy sector. In fact, a recent Searchlight Cyber report revealed the dark web regularly hosts auctions for initial access to energy companies – complete with an eBay-like 'Buy it now' option.
But, instead of new furniture, threat actors are selling items like bundles of company credentials with very-specific, sensitive information changing hands.
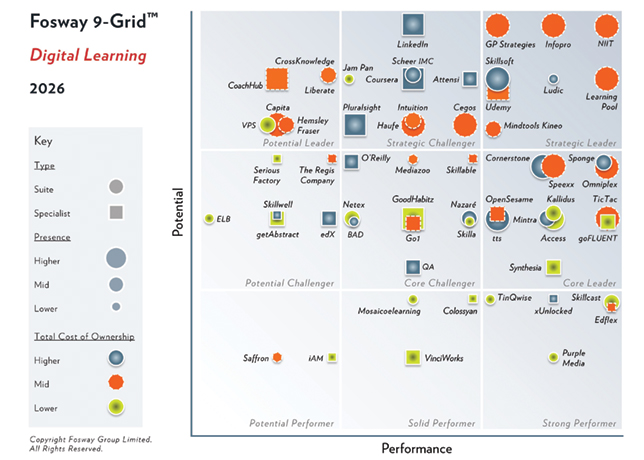
Graph 1 is an example of how these ‘adverts’ are presented:
Searchlight Cyber research found that oil, gas, and renewable energy companies in every corner of the globe, and every level of the energy sector are being targeted. Sale of remote access software and compromised VPNs are common.
Meanwhile, company email addresses, passwords, password-keys, and sensitive company data give buyers everything they need to launch an attack (Graph 2).
This is concerning, but, at least, there is a picture being painted. Knowing where vulnerabilities lie, what types of attacks are common, and what threats the industry regularly faces, means companies can fix gaps in their security systems and reduce the chance of significant issues.
DON’T WAIT TO REACT
Despite regular and known threats, plenty of oil and gas companies are missing the opportunity to mine the dark web for intelligence that they can use to get early warning sign of attack and inform their security strategies.
A study Searchlight Cyber conducted in 2023 shows that 27 per cent of oil and gas CISOs wrongly believe dark web activity has no impact on their company.
And, although 72 per cent of oil and gas companies do gather data from the dark web, this lags well behind other high-risk industries like manufacturing (83 per cent) and financial services (85 per cent).
Cybercriminals are always evolving their tactics, so organisations must keep pace with the latest techniques so they can react. In the security industry this practice is called threat modelling.
THREAT MODELLING USING DARK WEB INTELLIGENCE
Threat modelling is a crucial part of any security team’s plans to prevent attacks and maintain operational activity. It is how organisations can identify and quantify potential threats and vulnerabilities and decide where to prioritise time, money, and attention.
Incorporating dark web intelligence into threat modelling lets businesses stay ahead of cyber threats and reveals the full picture on emerging techniques. Done correctly, it delivers systematic analysis of attacker profiles relevant to them, likely attack vectors, and pinpoints which assets are most likely to catch the eye of attackers.
Analysing activity on the dark web also indicates the technical knowledge and experience of threat actors. With this information, energy organisations can build threat models to:
• Identify assets that could be targeted.
• Analyse weaknesses and countermeasures against threat actors.
• Understand trigger events that may lead to an attack.
• Create a comprehensive view of their threat landscape.
INTELLIGENCE-BASED DECISION-MAKING
When you know where you are most vulnerable, which new or previously unknown attack vendors are emerging, and when attacks may occur, you can better prepare.
Accordingly, a threat model using dark web insights means security teams can mitigate potential threats before it’s too late.
Any threat model should constantly be updated to keep pace with the evolution of cyberattacks. There are always new attackers and more sophisticated methods emerging.
Dark web threat intelligence is an integral part of any security plan for energy sector organisations.
Monitoring the place where cybercriminals conduct operations can greatly reduce the impact of threats and disruption to operations by filling knowledge gaps to support strategic and operational decisions.
It is only by understanding where you are at risk that you can adapt and evolve, to keep pace with threat actors.